A pharmacist inputs a 30-day prescription as four weekly prescriptions—quadrupling the Medicaid dispensing fees; a fraud ring obtains a list of Medicare patients who recently underwent hospital outpatient procedures and submits new phony claims; a chiropractor bills for spinal manipulations three times per week on every family member, including the children, until each member has its plan benefits exhausted.
What do all these stories have in common?
They are all real stories of improper billings spotted with data-driven methods, regardless of whether they can technically fit the definition of “fraud” (intent to receive undue financial gain which must be proven in a court of law).
The historical emphasis at health plans to focus on solely fraud and prosecutions is beginning to change to a more enterprise-wide approach to containing health care costs. The new label for those efforts is sometimes referred to as “payment integrity,” a term that more broadly encompasses the work done by fraud investigators, nurse reviewers, clinical edits, auditors, pre-payment review areas, and overpayment recovery groups. Payment integrity may also include subrogation and coordination with other benefit programs, depending on the health plan.
One such SAS customer, Blue Cross Blue Shield of Michigan, is evolving the use of advanced analytics collaboratively, across its enterprise, with SAS Fraud Framework for Health Care. Corporate Financial Investigations (CFI), pharmacy services, audit and payment integrity departments, and medical policy areas all are beginning to use analytics on the same data sets to address customer needs and root out potential fraud, waste and abuse.
It is what their customers expect. They have an oversight committee to review and evaluate alerts with each organizational department represented. Other areas such as claims processing, customer inquiry, subrogation, and human resources refer matters to CFI for potential investigation.
Whatever the flavor of payment integrity at a specific payer, historically, both the public and private sector have relied upon tips, business rules, and outlier models to mine claims data for suspicious issues.
Other sources of valuable data are often ignored since they may reside in different departments or were pulled for different business reasons. As a result, if the creative billers are effective at moving the activity around, and engaging multiple parties in the scheme, those historical methods may miss alerting an investigator or auditor.
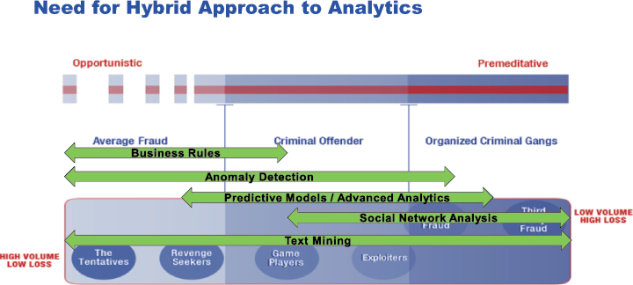
Since payment integrity issues are a spectrum of behavior, from the one-off cases where someone is seeking revenge or testing the system, all the way to organized, professional criminal networks, including internal and external parties on the payroll, the forward thinking payer needs to embrace many different approaches to data analytics in order to robustly detect the activity. See figure one below.
But becoming data-driven represents an evolution for the payer; an evolution from relying on an experienced investigator or clinician’s expert judgment to a data-driven approach, where you can let the data actually tell you where to focus the precious resources.
BCBSM’s CFI will analyze the data produced by the SAS solution; compare it to known fraud schemes and other internal data sources. The oversight committee will triage the alerts making a determination if the information suggests fraud, waste or abuse. If the issue is fraud, an intelligence package will be created for the investigator. This information will assist management with decision making in case assignments to determine priority of the case, resources required, the extent of the potential fraud across all lines of business and help determine compliance reporting requirements for government programs. Information derived from the SAS solution will lend clarity to the many puzzle pieces of the complex fraud schemes that are often tedious to assemble with traditional investigative techniques.
The oversight committee will direct abuse indicators to the audit department for their attention and waste indicators to the payment integrity department to determine if there are weaknesses in the claims system that are being leveraged.
Cooperation among different departments helps to reduce complexity in the organization and allows for several departments to rely on a single source of data. It provides a common decision making process rather than having individual areas working independently and failing to share their discoveries.
The goal is to interrupt fraud, waste and abuse as early in the cycle as possible using the SAS hybrid approach. This effort will save customer’s money, reduce the cost of remediation efforts and ensure the integrity of the provider community. A collaborative payment integrity approach creates value for the corporation and enhances customer satisfaction.
Advanced Analytics: Predictive Modeling
Predictive modeling improves the accuracy of detecting improper billings over rules and outlier analysis methods. Using data mining capabilities to detect statistical patterns in previous known suspicious behavior, models can assign a propensity score on new claims that have the same or similar characteristics, which prioritizes those new claims with the highest probability of inappropriate billing.
Predictive modeling is also superior to rules-only approaches because the analyst need not define the specific criteria that can later be evaded, but instead the data will drive the identification and weighting of parameters that contributed to the aberrant billing pattern. In this way, the false positives can be reduced, sometimes dramatically, allowing the analyst to scrutinize the most important cases first. (The example of the chiropractor billing on every family member is an actual predictive model that SAS built for a health plan customer, which resulted in similar schemes like it on newer claims being prevented from payment, and the customer also made benefit policy adjustments to stop the bleeding.)
Employing varied predictive modeling techniques make it possible to identify the method that provides the best accuracy (lift in accuracy of scoring) and is most appropriate to the situation in question (depending on missing data, large number of variables, etc.).
By incorporating varied methods and the capability to compare and determine the most accurate method, this provides the best mechanism for reducing false positives. The ability to test various methods also provides the ability to frequently re-evaluate the methods to prevent the analysis from degrading over time. All predictive models degrade over time; a model that has a 99% predictive capability today may have only 20% the efficacy five years from now as the billing behavior changes, and thus, no predictive model should be put on auto-pilot without being re-tested and tuned every few months.
Improper payments that are investigated and the outcomes of that process provide a valuable source of training data that will improve the accuracy of predictive models over time. Once that feedback loop is made available, the models become smarter. An audit trail is created as the model is phased into production and the predecessor model is retired. That is how health plans can evolve over time from being 90% based on someone’s expert judgment to being 90% data-driven. (In other words, there is never a scenario where expert judgment can be eliminated altogether.)
Advanced Analytics: Social Network Analysis
Social Network Analysis (also called link analysis) has become a recently popular analytical method and a necessary tool in spotting complex collusion schemes. While technology is now available to incorporate this in a data-driven way, savvy investigators have been informally conducting link analysis manually for years.
At Blue Cross Blue Shield of Michigan link analysis has historically been accomplished similar to assembling pieces of a puzzle by taking small bits of information and trying to determine how they fit or link to other pieces. In one complex case numerous hours were spent with law enforcement drawing linkages on dry erase boards and constantly shuffling the relationships as new information was discovered. SAS Fraud Framework will provide an automated solution. In addition, investigators will be able to enter ancillary information into the system on individuals who are not providers or customers, typically recruiters, to help build a total picture.
As complex schemes become more prevalent the tracking of recruiters and customer migration patterns between providers, pharmacies and facilities helps to proactively move the investigative initiatives along parallel to or ahead of the fraud schemes.
Links can either be social or transactional. Social links help to identify the same individual or group of collusive individuals who share social attributes, like similar names, or they are married or share a phone number. Fuzzy matching algorithms are applied to sets of identifying attributes to recognize slight variations amongst the data elements that suggest the records are connected to one another, thus earning the name, fuzzy.
Some examples:
- Beth Smith and Smith Elizabeth could be the same person, but exact matching will fail to detect the similarity.
- One provider may recycle the same address used by another provider, with slight alterations. Or the old mailing address used by one provider could be the billing address or practice location for another provider.
- Sometimes the same individual uses his or her corporate identification number instead of the individual provider identifier for submitting claims.
The second way of linking is via transaction links, which highlight associations between entities who are involved in any common transaction. For example, if a home health agency has a claim for a beneficiary and there is another physician listed as the referring/attending physician on the same home health claim, they are connected to each other via a transaction link.
The ability to let the data and technology identify the network targets for review (called target identification) based on the grouped entities with the most propensity for suspicious activity, is a major differentiator of the SAS approach to social network analysis vs. other link analysis tools available on the market today which only promote linkage visualizations once you know where to look.
Advanced Analytics: Text Mining
Finally, we come to the most underutilized method of advanced analytics in text mining of unstructured text. Some sources say that 80% of a health plan’s data remains in the unstructured text. Most anything in free form text can be parsed and analyzed with the appropriate text mining functionality. This opens up the use of a world of data in analytics beyond just claims data.
Electronic medical records can be reviewed to determine if there are too many overweight diabetics receiving the same treatment on the same day, because records are actually being copied. Call center logs can be analyzed to see if the same physician’s office is calling in to determine remaining benefit limits on every family member in the same week. Nurse notes transcribing the pre-certification call before the hospitalization can be compared to how the claim was billed to determine if any misrepresentation of condition occurred during that call. Grievance and appeal records can be examined to determine if the claim was refiled with different coding after an unfavorable denial was made. Imagine the possibilities.
Blue Cross Blue Shield of Michigan sees specific applicability of text mining in a number of ways. Unscrupulous providers will frequently probe the claims system refining rejected claims until they find the right combination of diagnosis and procedure codes that will cause payment. Reviewing rejected and approved claims with text mining functionality will help identify fraud indicators.
Text mining will also help ensure submission of an appropriate diagnosis code supporting an appropriate procedure code with the implementation of ICD-10 as the array of diagnosis codes expands exponentially.
Another example is a provider revising documented medical conditions or severity of illness on preauthorization requests until an expensive procedure such as a PET scan or MRI is authorized. Complacent providers will then rely on boiler plate language that previously resulted in payment on repeated future claims which can be identified with the text mining functionality.
Text Mining will assist with Risk Adjustment administrative decision making but also early flagging of fraud, waste and abuse indicators. A Risk Adjustment program spreads the financial risk of members as it “pools” or shares risk that lessens the impact of disproportionate health costs. Less healthy or sick individuals will have a higher risk score, while healthy individuals have a lower risk score.
The proper coding and medical necessity of these claims assists CMS in determining reimbursement to carriers. Medicare and commercial plans use medical records for the source of truth for diagnosis, while Medicaid uses medical and pharmacy claims. Text mining will ensure all data submitted on claims and through other supplemental means is accurately documented in medical records and is consistent with the diagnosis and procedure codes submitted.
New World Under Affordable Care Act
More than ever before, the issue of eligibility fraud is now front and center, as consumers struggle to determine their eligibility for different coverages and potential eligibility for subsidies. Of course, sadly, this opens the door to both those that have fraudulent intent, as well as just mass confusion. The ability to analyze income data, social links, and demographic data alongside claims data will provide another lens for payers looking beyond just integrity issues at claim time.
In the new Marketplace under the Affordable Care Act, will there be an incentive to apply for coverage just to exhibit drug seeking behavior, stock up on narcotics and then stop paying premiums? Will there be an incentive for other inappropriate overutilization of services, as a revenue generator for a health care provider’s offices, since the new world is guaranteed issue?
Many individuals will gain coverage as a result of the ACA, having been previously uninsured. Without a base line of the individual’s previous medical history carriers must be diligent to monitor these new entrants. Carriers must ensure that the newly covered are receiving appropriate care, if they entered the system to participate in fraud or are they misusing or overusing their benefits in a manner that suggests fraud, waste or abuse.
Plans are also responsible to report to CMS indicators that suggest fraudulent eligibility applications to gain subsidies. In addition, SIUs will be challenged with monitoring the migration of individuals from group coverage to individual coverage under the ACA to identify indicators of fraud. SIUs are taking on new roles by not only addressing claims fraud, waste and abuse but also addressing eligibility and the related compliance and integrity requirements of CMS for this new business.
There is no singular detection technique that is capable of systematically identifying the entire spectrum of improper billing activity, especially some of the fastest growing areas involving eligibility fraud, identity theft, and organized crime. It is only through the combination of multiple approaches that a highly organized scheme can be detected without the need for an inside informant.
A hybrid approach, which integrates rules, anomaly detection, powerful predictive analytics, modeling of relationships between entities, and text mining (so as to incorporate all the valuable data sources) is key to being proactive and containing costs. Blue Cross Blue Shield of Michigan is one such plan that is on the front lines in the war on improper payments.
Learn more about Bloomberg Law or Log In to keep reading:
See Breaking News in Context
Bloomberg Law provides trusted coverage of current events enhanced with legal analysis.
Already a subscriber?
Log in to keep reading or access research tools and resources.